Best Tools And Templates For Building Your Own Persistence System
In the rapidly evolving digital landscape of 2026, the concept of a “persistence system” has transcended simple database storage. Whether you are a software architect designing fault-tolerant data layers or a security professional developing modular Linux frameworks, building a custom persistence system is now a core requirement for operational continuity.
Persistence is the ability of a system to maintain its state, data, or access across restarts, crashes, or reboots. In today’s world of AI-driven infrastructure and edge computing, standard out-of-the-box solutions often fall short of specific performance and security needs. This guide explores the most advanced tools and templates to help you build a robust, high-performance persistence system from the ground up.
The Evolution of Data Persistence in 2026
Data persistence is no longer just about writing to a disk; it is about ensuring data durability across distributed environments. As we move further into 2026, the integration of real-time stream processing and persistent memory (PMEM) has changed the architecture of modern applications.
Essential Tools for Data Persistence
To build a modern data persistence layer, you must leverage tools that support high-availability and low-latency operations:
- RisingWave: A cloud-native streaming database that excels in providing persistent state for real-time analytics. It allows developers to treat streams as tables, simplifying the persistence of complex event data.
- Redis Stack: Beyond simple caching, the 2026 iteration of Redis offers advanced Persistence-as-a-Service models, utilizing AOF (Append Only File) and RDB snapshots with zero-latency overhead.
- TiDB: An open-source, distributed SQL database that supports Hybrid Transactional and Analytical Processing (HTAP), making it a top choice for systems requiring massive scalability.
Building Security Persistence: The PANIX Framework
For security researchers and detection engineers, building a persistence system often refers to maintaining a foothold in a target environment for testing purposes. In 2026, the PANIX framework has become the gold standard for Linux persistence.
PANIX is a modular, highly customizable framework designed for security professionals to automate the creation of persistent backdoors and access points in Linux environments. It allows users to build “templates” of persistence that can survive deep system audits.
Why PANIX is a Game-Changer
The modularity of PANIX allows you to inject persistence into systemd services, cron jobs, or even kernel modules. By using pre-built templates, you can ensure your system remains active even after a full reboot or security patch. This is critical for Red Teaming exercises where long-term access is necessary to simulate advanced persistent threats (APTs).
Top Templates for Designing Your Persistence Layer
When building your own system, you don’t need to reinvent the wheel. Using proven architectural templates can save hundreds of hours in development and debugging.
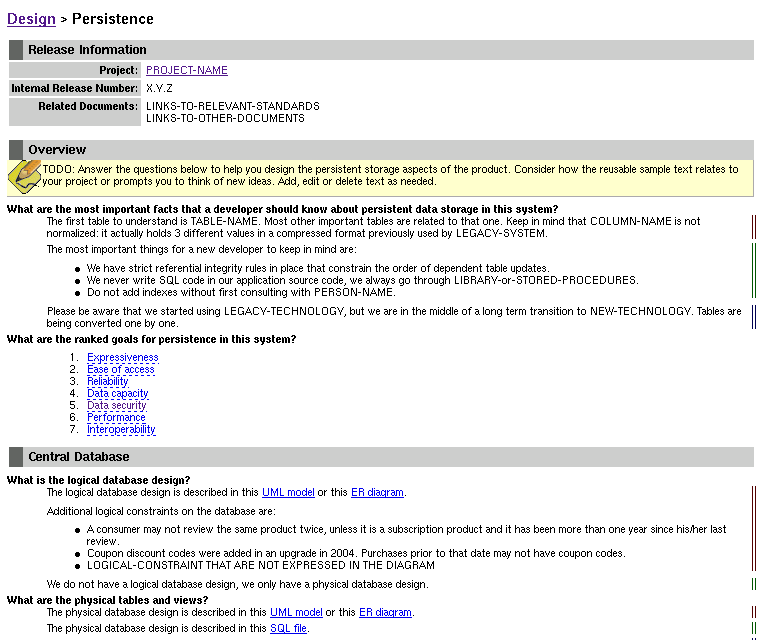
ReadySET Pro Persistence Design
The ReadySET Pro suite provides comprehensive product evaluation templates that include specific modules for persistence design. These templates help you map out how data moves from volatile memory to permanent storage, ensuring no data loss occurs during high-load spikes.
Modular Persistence Templates
- The Repository Pattern: A classic software design pattern that abstracts the data logic from the business logic. In 2026, modern implementations use dependency injection to switch between SQL, NoSQL, and Vector databases seamlessly.
- Event Sourcing Templates: Instead of storing just the current state, these templates persist a sequence of events. This is vital for audit trails and system recovery.
- Sidecar Persistence: Common in Kubernetes environments, this template uses a secondary container to handle data persistence, allowing the primary application to remain stateless and agile.
Analysis and Threat Hunting: Monitoring Your Persistence
Building a persistence system is only half the battle; you must also be able to analyze and monitor it. According to InfosecTrain, the rise of sophisticated malware has led to the development of powerful open-source tools for persistence analysis.
Best Tools for Persistence Analysis
- Autoruns (Linux/Windows versions): Still a staple in 2026, this tool identifies every program configured to run during system bootup or login.
- Osquery: Allows you to query your infrastructure as if it were a database. You can write SQL queries to detect unauthorized persistence mechanisms across thousands of endpoints.
- Auditd & Sysmon: These tools provide deep visibility into system calls, helping you track exactly how and when a persistence script was executed.
Best Practices for Building a Custom System in 2026
To ensure your custom persistence system is both performant and secure, follow these industry-standard best practices:
- Implement Zero Trust Persistence: Never assume that your persistent data is safe. Use AES-512 encryption at rest and ensure that only authenticated services can access the persistence layer.
- Automate Backups and Replication: Use tools like RisingWave’s replication engine to ensure that your persistent state is mirrored across multiple geographic regions.
- Use Immutable Infrastructure: In 2026, the most resilient systems are those that can be destroyed and rebuilt in seconds. Store your persistence configurations in version-controlled templates (Infrastructure as Code).
- Monitor for “Persistence Drift”: Regularly audit your system to ensure that no unauthorized persistence mechanisms (like those created by PANIX) have been introduced.
Conclusion: The Future of Persistence
Building your own persistence system in 2026 requires a blend of high-speed data engineering and robust security protocols. By utilizing modular tools like PANIX for system access and RisingWave for data durability, you can create a framework that is both resilient and adaptable.
Remember, the best persistence systems are those that are invisible to the end-user but indispensable to the system’s architecture. Use the templates and tools outlined above to start building a foundation that will stand the test of time and technology shifts.

